A: Ok, this question wins the “Thoughtful Question of the Week” award. Please forgive my more thoughtful (ie: long-winded) answer.
Although you and I may be able to dedicate tremendous time and energy to securing our devices and internet travels, we cannot do much about what happens to a web server that is out of our control and is involved in a data breach.
For example, let’s say we do online business with shoestringsrus.com (one can never have too many shoestrings). Then this weekend hackers somehow gain access to the shoestringsrus.com web server, including a dump of all 37 user accounts that have completed purchases on the site. The company webmaster maintained all user accounts data on the one device. This includes the user email address, password, credit card, purchase history, shipping address.
Even if the database is encrypted, the hackers have the time and resources to brute force the database password, and eventually gain full access to all of the data contained within.
Most people, once notified of the breach, would be concerned about their password getting out. But not you and me. Nope! That’s because we took the Practical Paranoia Security Essentials Online Course where we learned to create a unique password for every site and service just in case something like this happened. You see, if one uses the same password for most sites, then once one of those sites is breached, the hackers have software to use your email address and password to automatically attempt access to all banks, credit cards, and retailers in just seconds.
But if using the same password on many sites is dangerous, isn’t using the same username (almost always your email address) also a potential danger?
Yes, it can be. Not so much because of the automated attempts to access banks, etc., but because of social engineering and phishing. The hackers could use knowledge of your email address to target your email address and you with a tailored email.
Getting back to the question, no. You can’t prevent your email ID from being compromised any more than you can prevent your password from the breach. BUT… There is something you can do to help lessen the impact. This is done using a strategy similar to that used with passwords. Use a different email address for each site and service.
You don’t have to sign up for dozens or hundreds of email addresses. Instead, you can create aliases of your existing email. When using an alias, all email sent to the alias ends up in your normal inbox. Then by using your email app filters or rules, you can automate how these accounts are handled.
I visit and know such sites tend to fill up your inbox with junk. I will give this alias the name junk.marc@thepracticalparanoid.com. I can then create a rule or filter that says “if an email addressed to junk.marc@thepracticalparanoid.com is in the inbox, send it to the Trash”.
As another example, say I use the alias shoestringsrus.marc@thepracticalparanoid.com as my username/email address for my valued shoestringsrus.com account. If I get an email addressed to this alias that has nothing to do with shoestringsrus, I can be pretty sure they either sold my data or were compromised. This would be a good time to change my password with them.
HOW TO CREATE AN ALIAS
There are different ways to create an alias depending on where the email is hosted.
GOOGLE
In the case of a Google email which I use for marcmintz@gmail.com, periods are not recognized. So while marcmintz@gmail.com is the actual email, but I can make an instant alias simply by adding periods, such as: marc.mintz@gmail.com, m.a.r.c.m.i.n.t.z@gmail.com, etc. Note this does not work with personalized domains, such as marc@thepracticalparanoid.com.
Google also allows instant alias creation by using the + sign immediately after your name, and before the @ sign. So marc+mintz@thepracticalparanoid.com will come to my inbox with no further effort. This works for both @gmail.com and personalized domains.
OUTLOOK.COM
If you have an Outlook.com account, open a browser to https://account.live.com/names/Manage to add aliases to your existing account.
APPLE
If you have an @mac.com or @icloud.com email, you can use the + in the same way as with a Gmail account. But Apple includes an even better option they have named Hide My Email.
If you are running macOS 12 or iOS/iPadOS 15 or higher, Hide My Email can be found in Settings > Apple ID > iCloud > Hide My Email. If you are running an earlier OS, Hide My Email may be a great reason to upgrade.
With Hide My Email, you can have an unlimited number of randomly generated aliases, all pointing back to your @mac.com or @icloud.com inbox. But it does take a few minutes of preparation.
To set up Hide My Email:
- Open System Settings > Apple ID > iCloud > Hide My Email.
- Select the Options button.
- In the Hide My Email window, select + (Create New Address).
- A window opens with a new randomly generated address.
- Tap the Continue button.
- In the Label Your Address window, assign a Label and a Note to help remember how you are using the alias.
- From now on, this alias can be used anywhere an email address is requested, but you don’t want to reveal your real address.
OTHER EMAIL
If you use email from another hosting service, contact their technical support. Most do offer aliases, but each has a slightly different take on the process.
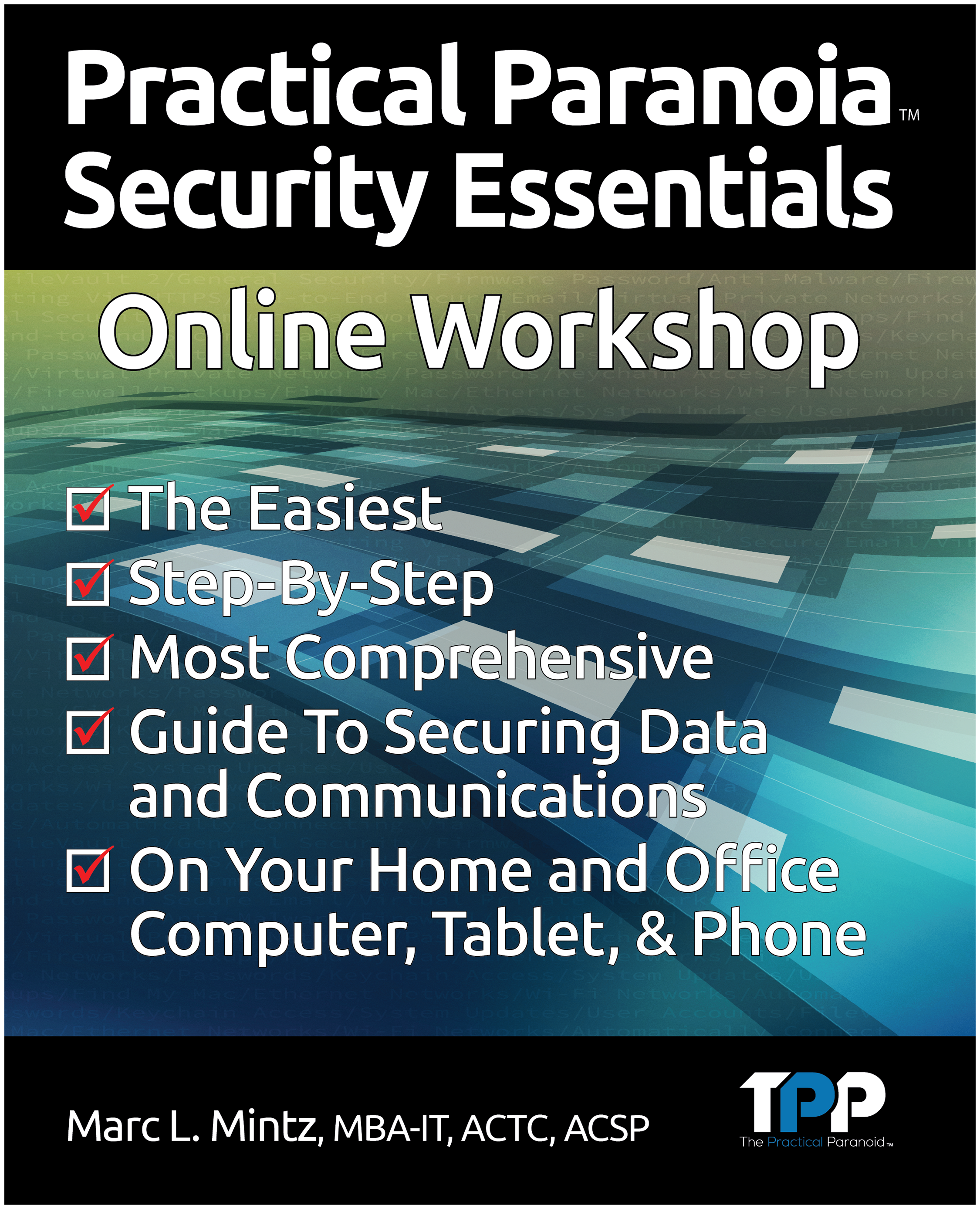
Practical Paranoia
Security Essentials Online Course
Starts March 6, 2023
The field of cybersecurity and internet privacy has for too long been the domain of the Information Technology elite. This has served to make their hourly rates beyond the reach of most of us mortals. And because almost everyone outside of the Fortune 500 lacks access to an IT Security Consultant, we pay another type of price:
- Only 5% of Companies’ Folder are Properly Protected (Forbes).
- Cyber Attacks are More Likely to Bring Down a Fighter Jet than Missiles (interestingengineering.com).
- Over 90% of all Healthcare Organizations Reported at Lease One Security Breach in the Last Three Years (beckershospitalreview.com).
- Cybercrime is Projected to Cost the World $10.5 Trillion Annually by 2025 (cybersecurctyventures.com).
- The Average Cost of a Data Breach was $3.86 Million in 2020.
- 95% of Cybersecurity Breaches are caused by Human Error (World Economic Forum).
- Data Breaches Exposed 22 Billion Records in 2021 (RiskBased Security).
- In 2021, 40% of Breaches Were Due to Phishing, 11% From Malware, and 22% From Hacking (Verizon).
- The Average Cost of a Data Breach to a Business is $4.24 Million in 2021 (IBM).
- The Average Time to Identify a Breach in 2021 was 212 Days (IBM).
- Personal Data is Involved in 45% of Data Breaches (Verizon).
- 56% of Americans Don’t Know What Steps to Take in the Event of a Data Breach (Varnish).
Cybersecurity and Internet Privacy impact each of us, often without even knowing it has happened!
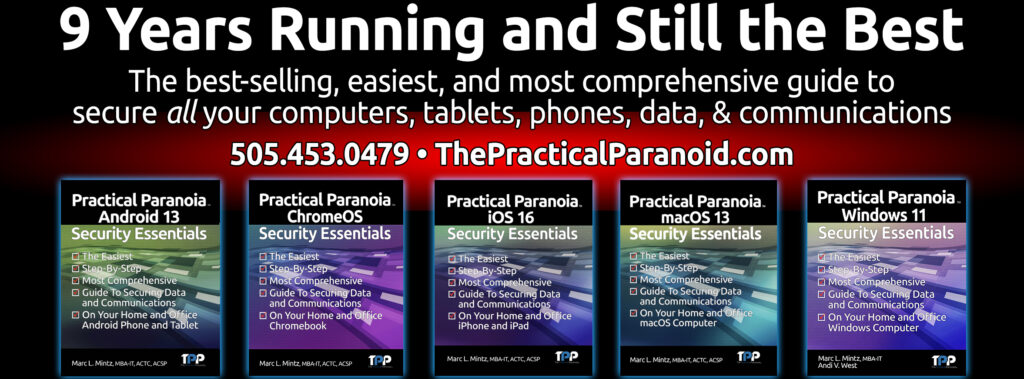
For over nine years The Practical Paranoid has published the best-selling, easiest, and most comprehensive guides to securing data and communications for both home and business users.
And now we are offering the same quick, easy, and accessible training we have provided to government, hospitals, businesses, and IT professionals to YOU! Our Practical Paranoia Security Essentials Online Course will take any user with basic computer skills, and give them the knowledge and skills to secure their device, data, and communications.
Our exclusive online course includes:
- A copy of Practical Paranoia macOS 13 Security Essentials book ($64.95 value) in LIVE! Format.
- LIVE! books are continuously updated until the next OS version is announced. They also allow the user to send the instructor questions directly from the book.
- The entire course in live Zoom format, accessible from your computer, smartphone, tablet, or Smart TV.
- Miss a live session? A recorded replay of each live session is available within 48 hours.
- Instructor available to answer your questions via Zoom.
- Certificate of Completion mailed to you at the completion of your course.
This course is normally offered at $275 per participant. But, if you order before March 1, 2023 a $200 discount will be applied making your total cost just $75!
GUARANTEE
After completing this course if you do not agree that this is the easiest and most comprehensive program of its kind, we will issue a full refund.
Visit https://thepracticalparanoid.com for more information and to register.