July 4th – Biggest Announcement EVER from The Practical Paranoid
Click the Play button below for the audio version of this posting.
On the Fourth of July, Americans celebrate independence, declaring we are no longer subject and subordinate to the monarch of Britain.
But today we are subject to greater tyranny through constant internet surveillance and breach of our online privacy. We are at the mercy of our government, Facebook, Google, cyber criminals, and other bad actors intent on knowing, seeing, and recording our every digital nanosecond.
Time for an updated Independence Day.
I’m Marc Mintz, Project Director for The Practical Paranoid (TPP).
TPP and I have worked to enlighten the public that it does not take an Apple Genius, Google Guru, or a Microsoft Engineer to secure your systems, data, and communications. Almost everything the government and big business do to ensure their cybersecurity and internet privacy can be done for you, by YOU, for less than what we spend on coffee. And in just a few hours.
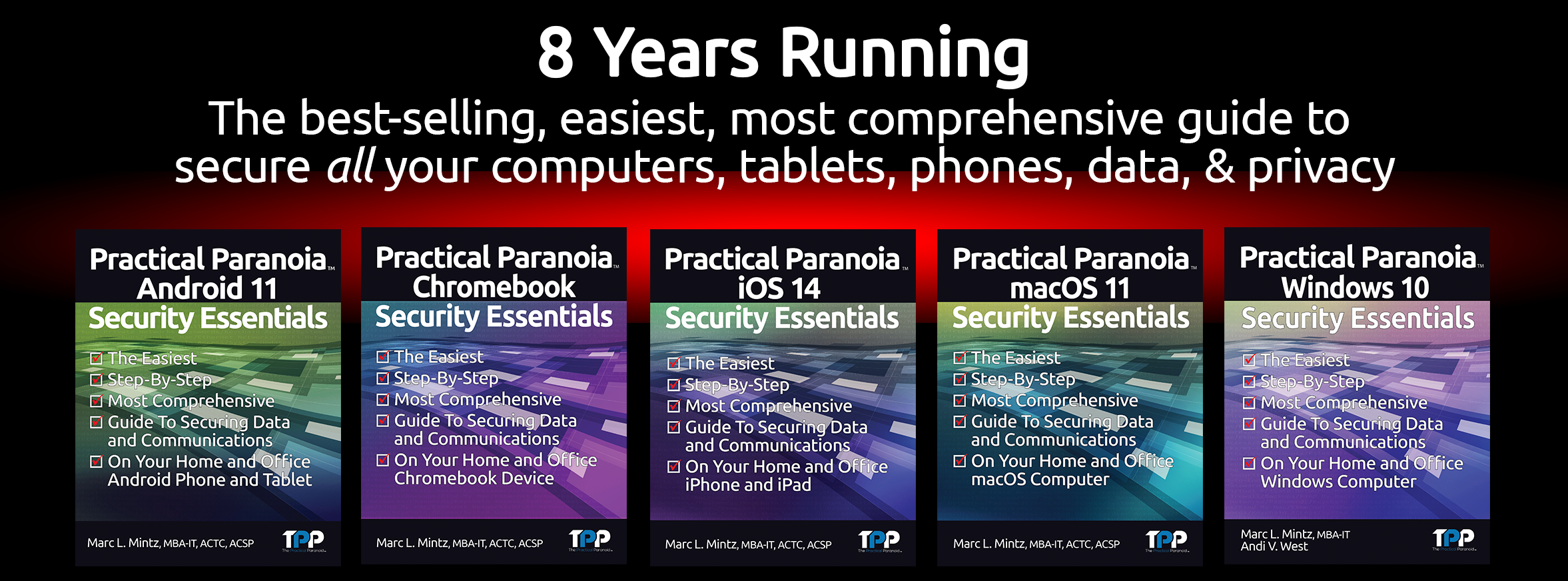
Our Practical Paranoia Security Essentials books have been showing non-technical users how to do this for over eight years.
The number one comment we receive from buyers of Practical Paranoia Security Essentials books is how surprised they are at how fast and easy it was to secure their phone, text, email, browsing, and entire digital life.
Yay!
The second most common comment from buyers is how intimidating Practical Paranoia books appear. Some buyers never jump into using a book after they purchase it.
Ouch!
With release of five new operating systems this year – Android 12, Chrome OS, iOS 15, macOS 12, and Windows 11 – we needed to remove the intimidation factor so that everyone could learn how to protect their data, communications, and privacy. And we did it.
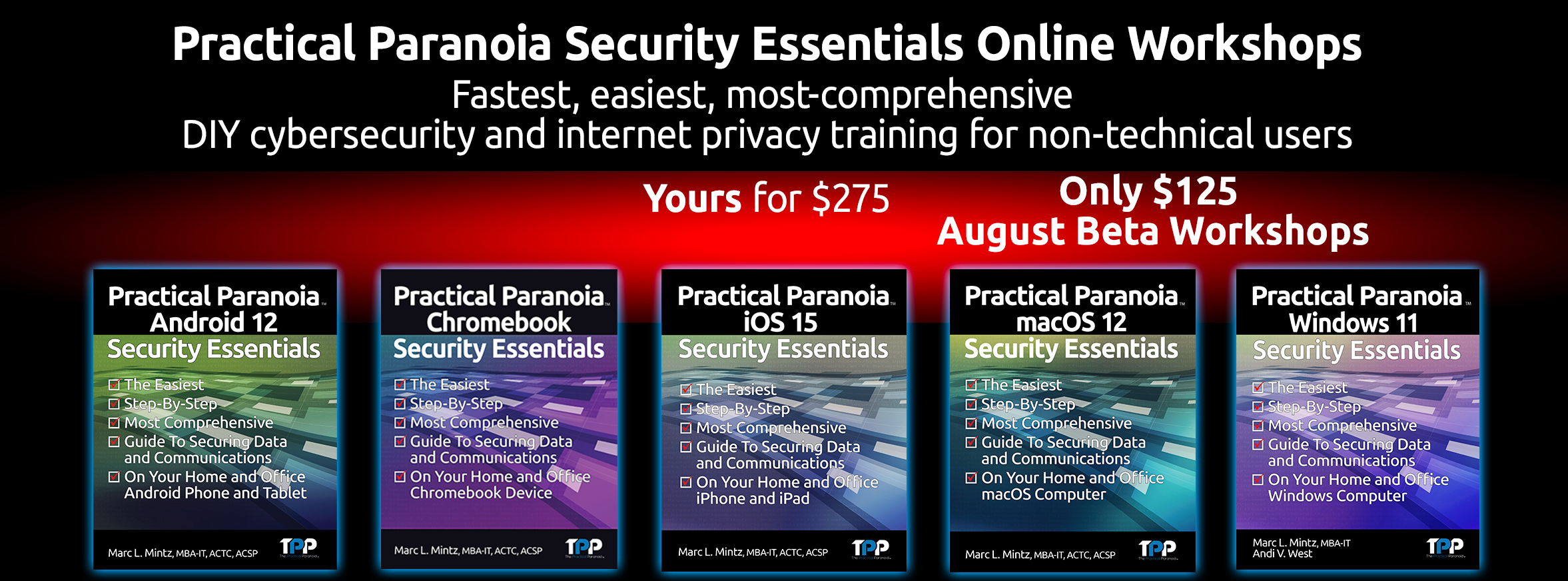
Announcing five brand-new Practical Paranoia Security Essentials Online Workshops that cover all the new OS products.
Protecting your digital life is as important as locking your home and carrying a driver’s license.
There are three paths to cybersecurity and internet privacy:
- You can pay a certified cybersecurity professional to do all the work that you will do in a TPP workshop. But pros cost $1,000-$4,000.
- You can buy the Practical Paranoia book and DIY for only $64.95. But you would have done it already if it weren’t for that pesky intimidation factor.
- Now you can do the work on your own–but with an industry leader guiding you in a workshop– the only workshop of its kind available anywhere at any price.
Think you don’t have the skills or background knowledge to do your own cybersecurity? We designed each workshop for the non-technical computer, tablet, and smartphone user. If you can tap, double-tap, and save a file, this course was made for you!
Each OS workshop consists of:
- A series of 7 to 10 one-hour classes on Zoom
- A copy of the latest best-selling TPP book, a $64.95 value
- Our August beta workshops will be presented live by an industry expert who has taught technology courses internationally
- Each class is recorded for students to access if they miss the live session
- Easy hands-on assignments to harden your security and privacy to industry standards
- AND Private Instructor Hours via Zoom to help you over any rough patches
The Practical Paranoia Security Essentials Online Workshops are only $275. And, it gets even better!
If you register for any of our first beta workshops in August 2021, your cost is only $125 for any workshop. Registration for beta workshops is limited and will close quickly.
Protecting you, your family, and your business cybersecurity and internet privacy is fast, easy, and inexpensive. You may even have fun doing it!
Visit https://thepracticalparanoid.com
for more information and to register for a one of a kind experience.